
A new relay attack has demonstrated that Tesla vehicles can be stolen with a quick hack, but thieves need to work in pairs and get as close as two inches from your phone or key card.
Security researchers at IOActive reverse-engineered Tesla’s NFC protocol and have demonstrated a new relay attack:
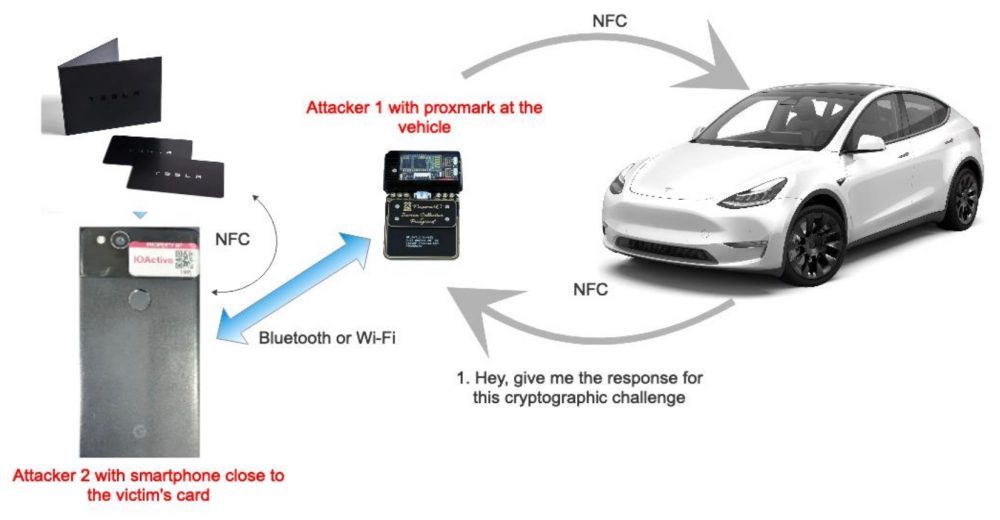
To successfully carry out the attack, IOActive reverse-engineered the NFC protocol Tesla uses between the NFC card and the vehicle, and we then created custom firmware modifications that allowed a Proxmark RDV4.0 device to relay NFC communications over Bluetooth/Wi-Fi using the Proxmark’s BlueShark module.
After having the protocol, the security researchers can build a device to quickly replicate the signal and send it to another NFC-enabled device.
IOActive describes the attack in a white paper:
This relay attack requires two attackers; in this case, one of the attackers will be using the Proxmark device at the vehicle’s NFC reader, and the other can use any NFC-capable device (such as a tablet, computer, or for the purposes of this example, a smartphone) close to either the victim’s Tesla NFC card or smartphone with the Tesla virtual key. The Proxmark and the second attacker’s smartphone can communicate via Bluetooth using the BlueShark module for the Proxmark RDV4.0, or even via Wi-Fi, connecting the Proxmark to a tiny computer like a Raspberry Pi or similar with Bluetooth while the Raspberry Pi connects to the second attacker’s smartphone via Wi-Fi.
They released a video demonstration of the hack on a Tesla Model Y:
While the attack does show a vulnerability, the thieves need to get the device within two inches of the owner’s key card or phone.
The security researchers noted that they believe that the hack can be achieved with longer distances between the device and the key using Bluetooth, but they haven’t demonstrated that.
A Tesla vehicle was recently used to demonstrate a Bluetooth hack that can unlock cars.
Thefts of Tesla vehicles are quite rare in North America, but in Europe, they have some more sophisticated thieves that managed a string of Tesla vehicle thefts through relay attacks, like this new one.
In response to those attacks, Tesla started rolling out extra layers of security with an “improved cryptography” key fob and optional “PIN to Drive” feature. Once applied, these measures can greatly decrease the chances of your Tesla vehicle being stolen.
In this case, on top of the PIN to Drive feature, drivers can carry their Tesla key card in an RFID card holder to protect against the attack, but it wouldn’t apply if you use your phone as a key, which is what most Tesla owners do.
FTC: We use income earning auto affiliate links. More.






Comments